SAML 2.0 vs OAuth 2.0 are both security protocols that enable users to access applications without separate passwords, but one confirms identity, the other delegates resource access. Conflating them produces architecture mismatches that are expensive to unwind. The table below resolves the core confusion immediately.
At a Glance: SAML 2.0 vs OAuth 2.0
| Dimension | SAML 2.0 | OAuth 2.0 | OAuth 2.0 + OIDC |
|---|---|---|---|
| Primary Purpose | Authentication / SSO | Authorization only | Authentication + Authorization |
| Data Format | XML assertions | JSON (JWT) | JSON (JWT + ID token) |
| Token Type | SAML assertion | Access token | Access token + ID token |
| Browser Dependence | High, redirect-only | Lower | Lower |
| API Suitability | Limited | High | High |
| Mobile Support | Indirect | Native | Native |
| Identity Attributes | Rich (roles, groups, custom) | None | Standard claims (OIDC spec) |
| Common Compliance Use | FedRAMP, HIPAA (XML signature covers full message) | Fragmented layers | Fragmented layers |
Why the third column matters: OAuth 2.0 is almost never deployed alone for SSO. Real-world architectures use OAuth 2.0 + OpenID Connect (OIDC). Treating them as independent is the most common mistake in protocol comparisons, including most vendor documentation.
How Do the Flows Actually Work Behind the Scenes?
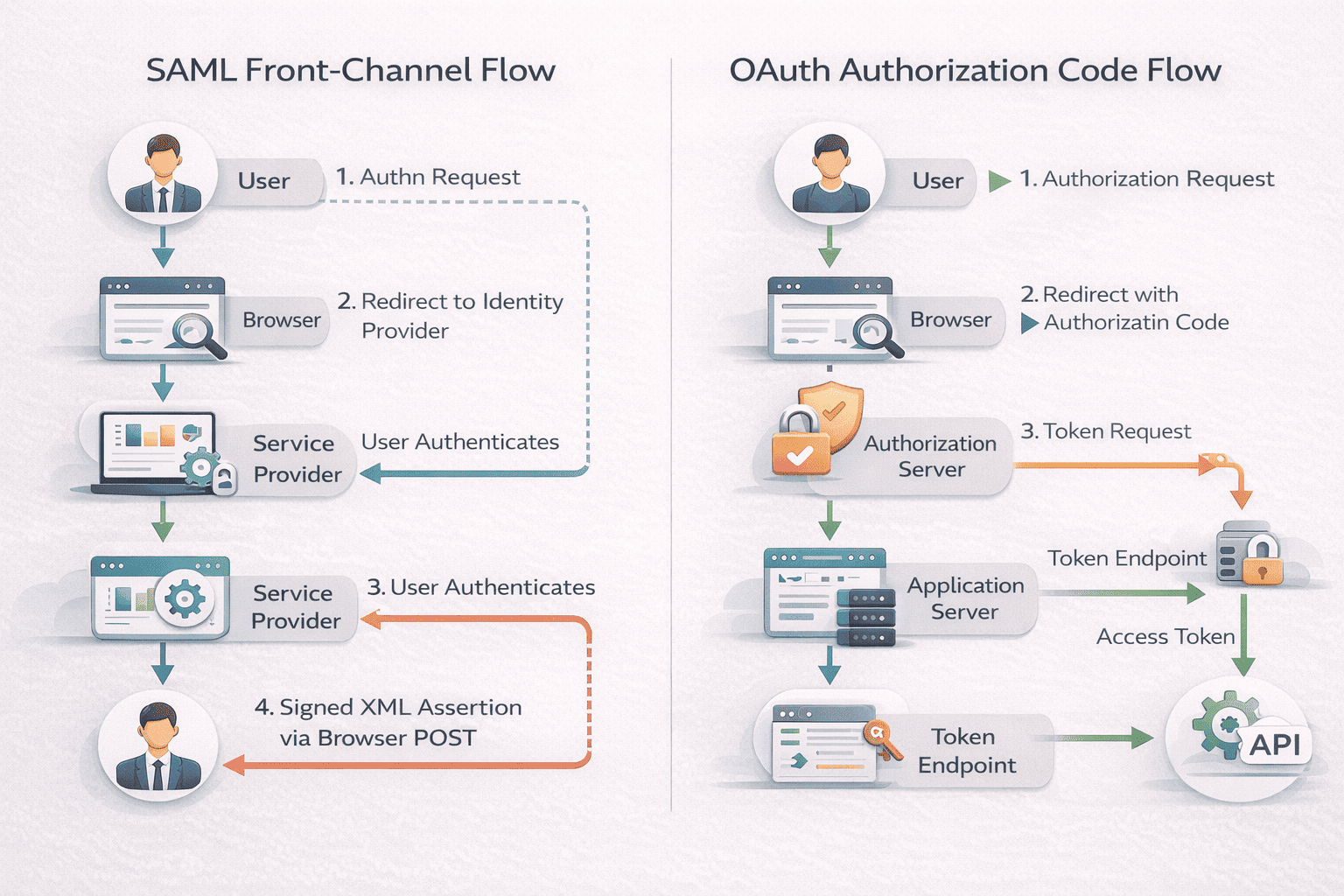
The critical architectural difference isn’t the steps, it’s who carries the data and over which channel. SAML uses the browser for everything. OAuth splits the work between front-channel (browser) and back-channel (server-to-server). This distinction has direct security and mobile-support implications.
| Protocol | Channel Model | Explanation |
|---|---|---|
| SAML | Front-Channel Only (Browser Carries Everything) | The browser physically carries the XML assertion at every step. The assertion is visible in browser history, subject to browser-level attacks, and requires a browser at all times, which is why native mobile apps can’t use SAML without embedding a webview. |
| OAuth 2.0 | Hybrid Front-Channel + Back-Channel | The access token never passes through the browser. The authorization code that redirects via browser is worthless without the client secret, it’s a one-time, short-lived reference, not a credential. The actual token exchange happens server-to-server over TLS. This back-channel design is why OAuth handles API authorization safely at scale. |
OIDC adds one element to the OAuth flow: The token endpoint returns an additional ID token (a signed JWT containing user identity claims: sub, email, name, issued by the authorization server) alongside the access token. The ID token is the authentication layer. The access token is the authorization layer. Together, they do what SAML’s assertion does, but through a decoupled, API-friendly mechanism.
The key insight for architects: SAML’s front-channel model makes it transparent and auditable (every assertion passes through the browser, creating a clear trace) but inflexible. OAuth’s back-channel model makes it secure for API contexts and mobile (tokens never expose to browser) but requires more components to reconstruct a complete audit trail.
Security Warning: What Actually Goes Wrong -SAML 2.0 vs OAuth 2.0

The generic answer is “security depends on implementation.” The expert answer: each protocol has a dominant failure mode that accounts for the majority of real-world breaches. If you’re deploying either protocol, these are the specific risks to build safeguards against first.
SAML’s #1 failure mode: Certificate expiration + XML Signature Wrapping (XSW)
In our experience auditing enterprise SSO configurations, expired X.509 certificates are the single most common SAML vulnerability, not because organizations don’t know certificates expire, but because SAML metadata gets configured once, works reliably for years, and then gets forgotten. Certificates typically expire in 1-3 years. When they do, one of two things happens: authentication breaks (which IT scrambles to fix under pressure) or, in misconfigured Service Providers, signature validation silently stops, creating an authentication bypass where unsigned assertions are accepted.
The more sophisticated threat is XML Signature Wrapping (XSW): by manipulating the structure of the XML document without invalidating the original signature, attackers can insert malicious content that gets processed as legitimate. Multiple IdP implementations, including historical versions of enterprise platforms, have been vulnerable to XSW. Proper countermeasure is strict schema validation and canonical XML processing. Most enterprise implementations don’t verify this is configured correctly after initial deployment.
SAML’s compliance advantage: The XML digital signature covers the entire assertion as a single cryptographic unit, providing message-level integrity. This is specifically why SAML is the preferred protocol in FedRAMP-regulated environments and DoD systems, the signed assertion creates a tamper-evident audit trail that satisfies authentication assurance requirements. OAuth’s security is distributed across TLS transport, token scopes, and client authentication, harder to present as a unified audit artifact.
OAuth’s #1 failure mode: Token theft via Open Redirect + Scope Creep
OAuth access tokens are bearer tokens: possession equals access. The most exploited attack vector is Open Redirect during authorization: if redirect URIs are configured with wildcard subdomains or insufficient validation, attackers redirect authorization codes, or in implicit flow, tokens directly to attacker-controlled endpoints. OAuth 2.1 mandates exact-match redirect URI validation specifically to close this vector.
The operational failure we see most frequently isn’t exotic; it’s Scope Creep: developers requesting admin: all when they need read: profile, or issuing tokens with 30-day expiration because refresh logic is inconvenient to implement. A broad-scope, long-lived token stored in browser localStorage is the highest-value target in the infrastructure. We’ve seen tokens granted to decommissioned applications remain valid for months because token revocation wasn’t implemented.
The net difference in attack surface: SAML vulnerabilities concentrate in XML parsing complexity and certificate lifecycle management, solvable through operational discipline. OAuth vulnerabilities distribute across grant type selection, redirect URI configuration, token storage architecture, and scope governance, requiring ongoing engineering attention. Neither is inherently safer; both require active defense. The protocol choice should match the team’s capacity to manage the specific risk surface.
Pros and Cons: Protocol Trade-offs
SAML 2.0
- Advantages: Strong enterprise SSO, rich attribute assertions, mature ecosystem, message-level integrity for compliance
- Limitations: XML complexity, less API-friendly, browser-heavy, certificate management overhead
OAuth 2.0
- Advantages: API-first design, mobile-friendly, scoped delegation, back-channel token security
- Limitations: Not authentication alone (requires OIDC), bearer token theft risk, grant type selection complexity, scope creep risk
Comparison Table: Enterprise vs API Environments
| Context | SAML Fit | OAuth + OIDC Fit |
|---|---|---|
| Enterprise SSO | Strong- designed for corporate web apps | Strong- with OIDC layer |
| API Access | Limited – awkward for programmatic calls | Strong- designed for APIs |
| Mobile Apps | Indirect- requires an embedded browser | Native- mobile-optimized |
| Microservices | Limited – not service-to-service | Strong- client credentials |
| Regulated (FedRAMP/HIPAA) | Strong- XML signature = message integrity | Moderate – fragmented security layers |
| Legacy Systems | Strong – established patterns | Moderate – newer protocol |
The Architect’s Decision Matrix: Business Constraints, Not Just Technical Fit – SAML 2.0 vs OAuth 2.0
Most protocol comparisons stop at “SAML for SSO, OAuth for APIs.” That’s sufficient for basic decisions. Real architecture choices are driven by constraints that the basic guides skip:
Regulatory compliance (FedRAMP, HIPAA, DoD)
SAML is explicitly preferred in FedRAMP-authorized environments because its XML digital signature cryptographically covers the entire assertion payload, entity ID, attributes, conditions, and the authentication statement, in a single verifiable envelope. OAuth’s security model distributes across TLS transport, token validation, and scope enforcement across separate layers. Auditors in regulated environments find SAML’s single-signature evidence easier to present than OAuth’s distributed security model.
Legacy identity infrastructure
Organizations with Shibboleth, ADFS, or early-generation Ping Federate installations face significant re-engineering costs migrating to OAuth/OIDC. If the IdP is already SAML-native and the SP integrations are mature, the TCO argument for staying on SAML is strong, especially if the use case is pure web SSO with no mobile or API requirements.
Greenfield cloud-native deployments
Modern SaaS platforms, developer tools, and API-first architectures assume OAuth+OIDC. Building SAML into a Kubernetes microservices environment requires browser-dependent flows that conflict with service mesh architecture. For organizations starting fresh, OAuth+OIDC is the default recommendation of the IETF, major cloud providers (AWS Cognito, Google Identity Platform, Azure AD), and the OAuth 2.1 security best current practices document.
Third-party delegation scenarios
OAuth was specifically designed for the “I want to grant App X limited access to my data on Service Y without giving App X my password” use case. SAML has no equivalent delegation model. If your use case involves users granting external applications scoped access to their data, GitHub OAuth apps, Google Workspace integrations, Salesforce Connected Apps, OAuth is the only practical option.
Mixed environments (the most common case)
Large enterprises rarely face a binary choice. The architectural pattern that emerges: SAML handles employee SSO for internal web apps (HR systems, enterprise SaaS), while OAuth+OIDC secures developer-facing APIs, mobile applications, and third-party integrations. The IdP (Okta, Azure AD, Ping) typically supports both protocols, issuing SAML assertions to legacy web apps and OAuth tokens to modern API clients from the same identity store.
Can SAML and OAuth Work Together?
Many enterprises deploy both, using each where it fits:
- Web SSO via SAML: Employees access SaaS applications through single sign-on powered by SAML assertions.
- APIs via OAuth: Same applications expose APIs accessed using OAuth tokens.
- OIDC bridges the gap: OpenID Connect uses OAuth with OIDC for both authentication and API authorization, gradually replacing SAML in modern environments.
The protocols aren’t mutually exclusive. Hybrid infrastructures use SAML for employee SSO and OAuth for APIs, mobile apps, third-party integrations.
The Architect’s Decision Matrix: Business Constraints, Not Just Technical Definitions
Most protocol comparisons stop at feature lists. The more useful question is: which non-technical business constraints force one choice over the other?
Choose SAML when:
- FedRAMP or DoD compliance is required. SAML’s XML digital signature cryptographically covers the entire assertion payload as a single, tamper-evident unit. This message-level integrity satisfies FedRAMP requirements around authentication assurance and audit trail continuity. OAuth’s security model is layered across TLS transport, token scopes, and client authentication, auditors reviewing these systems must trace security guarantees across multiple components rather than one signed document. For government contractors and defense vendors, SAML’s monolithic signature model is frequently the path of least resistance through compliance review.
- Your IdP is the organizational authority for identity. SAML was designed for federated trust between distinct organizations, a university federating with research institutions, or a hospital network sharing identity across partner facilities. If the architectural requirement is “our HRIS owns the authoritative user record and everything else trusts it,” SAML’s IdP-SP trust model is a direct fit.
- Legacy enterprise stack. Organizations with 10+ year-old Shibboleth, Active Directory Federation Services (ADFS), or PingFederate deployments have SAML metadata configurations for hundreds of applications. Migrating to OAuth/OIDC requires rebuilding trust relationships with every Service Provider, a 12-18 month project for large enterprises. SAML’s maintenance cost is lower than migration cost in these environments.
Choose OAuth 2.0 + OIDC when:
- API-first or mobile-first architecture. OAuth tokens work natively in Authorization: Bearer HTTP headers. Mobile apps use PKCE (Proof Key for Code Exchange) flows that don’t require browser redirects. If your architecture involves REST APIs, microservices, or native mobile applications, OAuth is the design-time default, forcing SAML into these contexts requires workarounds that add complexity without benefit.
- Third-party delegation is a core requirement. OAuth was designed for “user grants third-party app access to their resources.” GitHub Actions accessing AWS, Zapier integrating with Salesforce, a mobile app reading Google Calendar, these delegation patterns are native OAuth use cases. SAML has no equivalent delegation model.
- Greenfield cloud-native environment. If you’re building on AWS Cognito, Azure Entra ID with modern authentication, or Auth0/Okta with OIDC flows, the platform defaults favor OAuth+OIDC. Running SAML on these platforms is possible but introduces configuration overhead that the modern stack doesn’t require.
The hybrid reality: Most enterprises above 1,000 employees run both. SAML handles corporate SSO for employee-facing applications (the IdP is the HRIS or AD). OAuth+OIDC handles developer-facing APIs, mobile apps, and third-party integrations. The decision isn’t binary, it’s which protocol handles which trust domain.
SAML 2.0 vs OAuth 2.0 at Scale – Structural Summary
SAML 2.0 vs OAuth 2.0 comparison reveals:
Different purposes: SAML provides authentication; OAuth provides authorization
- Different structures: SAML uses XML assertions; OAuth uses JSON tokens
- Different environments: SAML fits web SSO; OAuth fits APIs and mobile
- Often coexist: SAML for employee SSO, OAuth for API security
- Security depends on configuration, not protocol choice
How to Think About Choosing Between SAML and OAuth
- Are we solving authentication or authorization? If confirming user identity for SSO, SAML fits. If granting applications access to resources, OAuth is designed for that.
- Is this web SSO or an API problem? Web-based employee access to SaaS suggests SAML. Programmatic API access, mobile apps, or microservices suggest OAuth.
- Are we in a legacy enterprise stack? Established SAML infrastructures have lower switching costs. Greenfield deployments favor OAuth flexibility.
- Do we need delegated third-party access? OAuth is the standard framework for users granting external applications limited access. SAML doesn’t model this pattern.
- What technical expertise is available? SAML requires XML parsing, certificate management. OAuth requires understanding grant types, token lifecycle. Match protocol to team capability.
FAQ
Q1. What is the difference between SAML and OAuth?
SAML is an authentication protocol for single sign-on confirming user identity through XML assertions. OAuth is an authorization framework for delegated access granting limited permissions through access tokens. SAML answers “who is this user”; OAuth answers “what can this request access.”
Q2. Is OAuth replacing SAML?
No. OAuth with OpenID Connect handles some SSO use cases, but SAML remains dominant in enterprise environments. Many organizations use both: SAML for corporate SSO, OAuth for API and mobile access. Reality shows coexistence based on use case fit.
Q3. Which is more secure, SAML or OAuth?
Neither is inherently more secure. Security depends on implementation: proper certificate management (SAML), secure token storage (OAuth), TLS configuration (both), and regular audits. Misconfiguration creates vulnerabilities in either protocol.
Q4. Can SAML be used for APIs?
Technically possible but impractical. SAML assertions are browser-centric, XML-heavy, designed for web SSO. APIs require lightweight, programmatic authorization, OAuth’s strength. OAuth’s token-based model fits API architectures more naturally.
Q5. Does OAuth provide authentication?
Not by itself. OAuth 2.0 provides authorization (access delegation) but not authentication (identity verification). OpenID Connect extends OAuth with ID tokens containing user identity, enabling authentication. When OAuth pairs with OIDC, it supports both.
Q6. What is OpenID Connect?
An identity layer built on OAuth 2.0 adding authentication capabilities. OIDC introduces ID tokens (JWT format) containing user identity claims alongside OAuth’s access tokens. This enables applications to verify user identity while maintaining OAuth’s authorization strengths.
Q7. Is SAML outdated?
Not outdated but narrower in scope than modern needs. SAML excels at enterprise web SSO, a use case that remains relevant. It doesn’t fit mobile, APIs, or microservices as naturally as OAuth. “Outdated” implies obsolete; SAML is “specialized” for specific environments where it remains standard.