LMS security & data privacy are often conflated, they aren’t the same problem. Security covers mechanisms preventing unauthorized access: authentication, encryption at rest and in transit, role-based access control, audit logging. Privacy covers lawful and ethical data handling: regulatory compliance, consent workflows, retention policies, and learner subject rights. A platform can be technically secure while being privacy non-compliant, retaining data beyond lawful basis, or transferring records without required agreements. Both failures carry consequences.
Three forces raise stakes in 2026: the distributed workforce accessing cloud LMS from personal devices; deep HRIS and identity integrations expanding data surfaces; and accelerating regulatory pressure from GDPR enforcement, HIPAA scrutiny, and emerging state privacy laws. A fourth force has emerged in 2026: generative AI integration. LMS features using LLMs to summarize learner responses, generate personalized content, or auto-grade assessments must be vetted for data leakage risks and learner opt-out rights, the EU AI Act now requires transparency about automated processing of personal data in high-stakes educational contexts, and India’s Digital Personal Data Protection Act (DPDPA) creates new consent obligations for platforms operating in that market. Organizations treating security as a checkbox and privacy as the legal team’s problem are building on unstable ground.
What Is the Difference Between LMS Security and LMS Data Privacy?

| Aspect | LMS Security | LMS Data Privacy |
|---|---|---|
| Core Question | “Can unauthorized parties access this system?” | “Are we handling personal data with lawful basis and proportionality?” |
| Focus | Prevent unauthorized access | Protect personal data rights |
| Tools | Encryption, MFA, RBAC, audit trails | Consent workflows, retention rules, deletion rights |
| Governed By | IT, security teams | Legal, compliance, DPO |
| Risk Type | Data breach, unauthorized access | Regulatory violation |
| Failure Consequence | Operational disruption | Fines, enforcement action |
A data processing agreement (DPA) with your LMS vendor is a privacy instrument. TLS encryption is a security instrument. Both matter; neither substitutes for the other.
How Secure Should Your LMS Really Be? Context Matters
| Context | Security Expectation | Privacy Sensitivity |
|---|---|---|
| SMB (<500 employees) | Basic SSO + TLS encryption in transit | Moderate – employee training records |
| Enterprise | Federated SSO, RBAC, 12-month audit log retention | High – HR data, performance-linked assessments |
| Healthcare | BAA-signed vendor, 6-year immutable audit logs, PHI-masking in learner records | Very High- patient-adjacent data, HIPAA breach notification |
| Education | FERPA controls, AI proctoring opt-out rights, no secondary data processing | High – minor records, EU AI Act proctoring restrictions |
| Regulated Finance | SOX/FCA alignment, tamper-evident log retention, role-based trade data access | High- training completion as compliance evidence |
Healthcare organizations handling patient-adjacent training data operate under HIPAA requirements, access logs become audit evidence, breach notification timelines are legally defined. Choosing an LMS vendor who hasn’t signed a Business Associate Agreement (BAA) is a compliance failure regardless of technical security quality.
Education institutions fall under FERPA, restricting disclosure of personally identifiable student information. Platforms must be assessed for what data they collect, where it’s stored, and who can access it. Over-engineering security for contexts that don’t require it creates adoption friction. Under-engineering for regulated contexts creates compliance exposure.
SaaS LMS vs On-Prem LMS: Which Is More Secure?
Neither is universally more secure. The difference is who owns which responsibilities.
| Deployment | Advantages | Limitations |
|---|---|---|
| SaaS LMS | Vendor-managed patching, built-in encryption, automatic updates | Less infrastructure control, data residency constraints |
| On-Prem LMS | Full data and infrastructure control | Heavy IT burden, manual patching, self-managed certificates |
SaaS platforms (Docebo & SimpliTrain for enterprise, Canvas LMS in education) offload infrastructure security to the vendor. The organization’s responsibility shifts to identity governance and verifying vendor posture through certifications (SOC 2 Type II, ISO 27001).
On-premise deployments (Moodle self-hosted) transfer full responsibility to internal IT, patch cycles, penetration testing, certificate rotation. Maximum control, maximum burden.
In practice, most SaaS LMS security failures trace to configuration and identity management gaps on the customer side, not platform vulnerabilities. Choosing SaaS doesn’t eliminate security responsibility; it shifts its location.
How Identity and Access Management (IAM) Impacts LMS Security
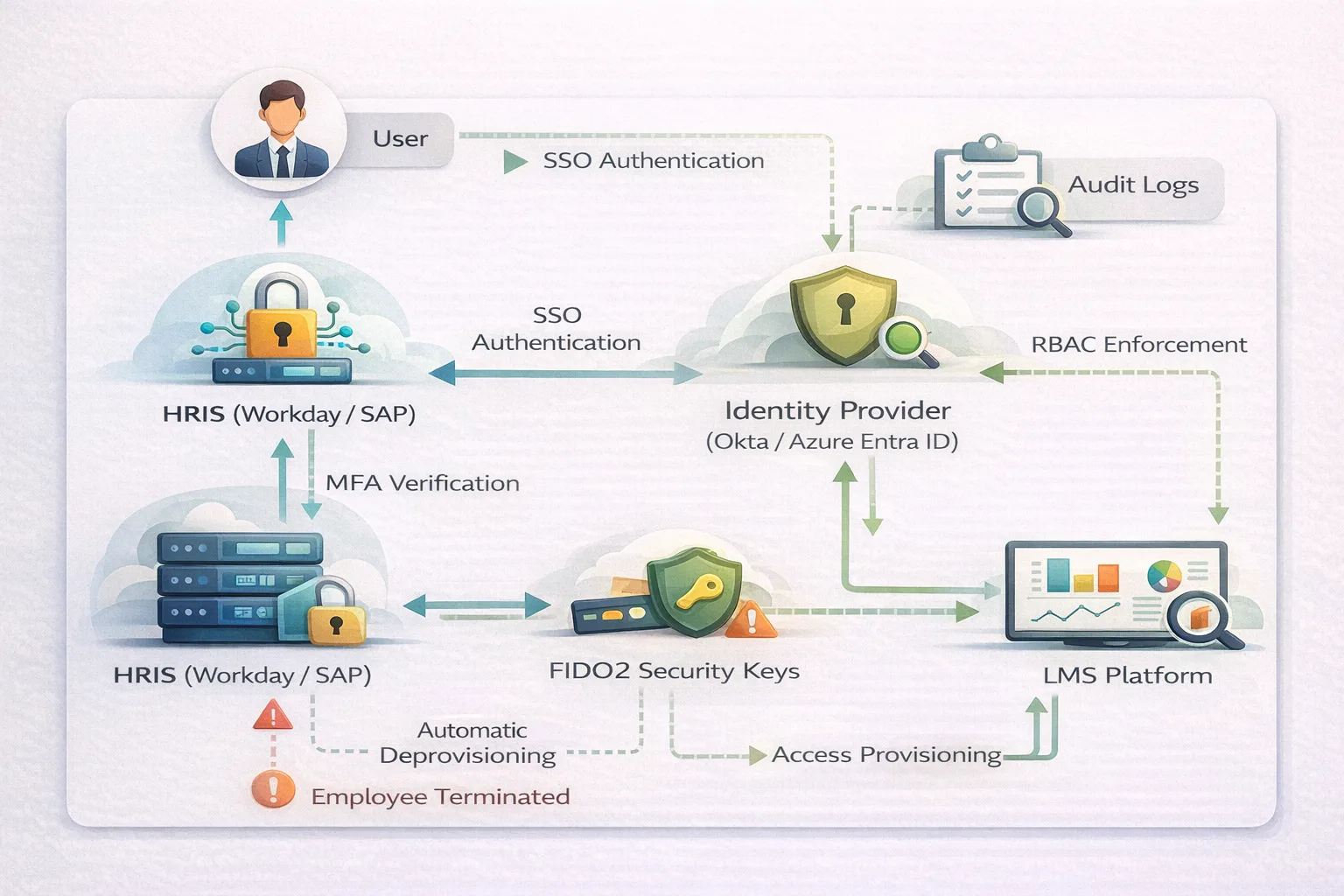
Single Sign-On (SSO): Integrating via SAML or OpenID Connect centralizes authentication and eliminates password proliferation. When employees authenticate against one identity provider (Active Directory, Okta, Azure Entra ID), credential management is consistent and auditable.
Multi-Factor Authentication (MFA): MFA is mandatory in 2026, but “Push Fatigue” has become a primary breach vector, attackers flood users with approval requests until they accidentally accept. Implement Phishing-Resistant MFA (FIDO2/WebAuthn) for all admin roles, where hardware security keys or device-bound passkeys eliminate push-based attacks entirely. For general learners, use Risk-Based Authentication (RBA), dynamically requiring MFA only when access patterns deviate from baseline (unusual location, new device, off-hours login) rather than on every session. This preserves learner experience without compromising the perimeter.
Role-Based Access Control (RBAC): Granular permission mapping ensures each role accesses only what it requires. A course author doesn’t need organization-wide reporting access. Role drift, accounts accumulating permissions beyond current job function over time, requires periodic access reviews, not just correct initial configuration.
Deprovisioning via HRIS integration: The most common enterprise LMS access governance failure is former employees retaining active accounts, including admin-level access, after termination.
Risk Insight
Internal audit data consistently shows that without HRIS-to-LMS automation, admin-level “orphan accounts” persist for an average of 14 days post-termination, a critical lateral movement window for attackers. A former admin who still holds LMS access after their Workday record is terminated can export learner PII, modify compliance completion records, or disable security controls. In regulated industries, this is not just an IT gap, it is a reportable audit finding and, in HIPAA contexts, a potential breach trigger if that account accesses learner health-adjacent records during the 14-day window.
HRIS-to-LMS synchronization closes this gap: termination in Workday or SAP triggers LMS account deactivation automatically, typically within the same sync cycle (real-time or nightly batch depending on configuration).
Data Residency and Cross-Border Compliance
LMS security & data privacy requirements often hinge on where data physically resides, not just how it’s secured. GDPR requires that EU learner data transfers comply with lawful transfer mechanisms (Standard Contractual Clauses, adequacy decisions). Storing EU records on US-only infrastructure without a valid transfer mechanism creates compliance exposure regardless of infrastructure security quality.
Practical LMS selection questions:
- Does the vendor offer EU-region hosting?
- Does learner data transit global CDN nodes outside the contracted region?
- Does the vendor provide a signed Data Processing Agreement (DPA)?
Healthcare, government contractor, and financial services training data may carry additional sector-specific data sovereignty requirements. Verify hosting architecture and sub-processor chains before signing, post-contract discovery is costly.
Audit Logs, Reporting, and Incident Response: The Overlooked Layer
Audit trails serve dual functions: security monitoring (detecting unauthorized access patterns) and compliance evidence (proving training completion to regulators).
What logs should capture: User authentication events, admin actions, data access, configuration changes.
The operational tension: Log retention creates cost-versus-compliance trade-offs. HIPAA requires 6-year retention of certain records; GDPR requires data minimization. Store based on regulatory requirement, not indefinitely.
Logs are only valuable if monitored. Define alert thresholds, bulk data exports, admin activity outside business hours, unusually high course completions in compressed time windows, before a breach makes logs forensic evidence rather than preventive intelligence.
2026 LMS Security & Privacy Audit Checklist
Use this as a baseline assessment before signing new vendor contracts or conducting annual governance reviews:
Identity & Access
[ ] SSO deprovisioning latency tested, accounts deactivate within one sync cycle of HRIS termination
[ ] FIDO2/WebAuthn MFA enforced for all admin roles
[ ] Risk-Based Authentication configured for learner roles
[ ] RBAC permissions reviewed in last 90 days for role drift
[ ] Orphan accounts (no HRIS record) identified and removed
Vendor Posture
[ ] SOC 2 Type II report dated within the last 12 months (not just “we have SOC 2”)
[ ] ISO 27001 certificate current and covers LMS data processing scope
[ ] Penetration test results available and actioned within last 12 months
[ ] Business Associate Agreement (BAA) signed if any healthcare-adjacent data flows through platform
Data Residency & Compliance
[ ] Sub-processor list reviewed, all data processors mapped to contractual regions
[ ] EU learner data confirmed to remain within EU or covered by valid SCCs
[ ] Data Processing Agreement (DPA) signed and reviewed by legal
[ ] AI-powered LMS features (summarization, adaptive content, proctoring) reviewed for EU AI Act transparency requirements and learner opt-out rights
Audit Logs
[ ] Log retention policy aligned to highest applicable regulatory requirement (HIPAA: 6 years; GDPR: minimum necessary)
[ ] Alert thresholds defined for: bulk exports, off-hours admin access, anomalous completion velocity
[ ] Log access restricted to authorized security/compliance personnel
Incident Readiness
[ ] Incident response plan includes LMS as named system
[ ] Breach notification timeline tested against GDPR 72-hour and HIPAA 60-day requirements
[ ] Backup authentication method exists if IdP/SSO experiences downtime
How to Think About LMS Security & Data Privacy Decisions
Five questions frame the architectural decisions before platform evaluation:
- What type of learner data do we collect? Completion records for mandatory compliance training carry different sensitivity than performance assessments tied to employment decisions. Data classification precedes security design.
- Who controls identity? If HRIS is the authoritative identity source, LMS security depends on synchronization integrity. External partners or customers without HRIS records require more complex identity management.
- What regulatory environment do we operate in? GDPR, HIPAA, FERPA, and SOX carry different requirements. Regulatory mapping determines minimum controls, everything else is operational judgment.
- Do we have internal IT resources? On-premise security requires dedicated engineering capacity. SaaS reduces infrastructure burden but doesn’t eliminate governance requirements.
- What happens if an audit occurs tomorrow? Can you produce 12 months of access logs? Demonstrate who has admin access and why? Show terminated employees were deprovisioned within 24 hours? Audit readiness is the operational test of governance maturity.
LMS security & data privacy are governance design problems, not feature selection problems. Security is not a feature, it is a governance design.
FAQ
Q1. Is cloud LMS secure?
Cloud LMS platforms can be highly secure, but “cloud” is a deployment model, not a security guarantee. Security depends on vendor infrastructure practices (SOC 2 Type II, penetration testing cadence) and organizational identity governance. Most cloud LMS security failures originate from misconfigured access controls or deprovisioning gaps, not platform vulnerabilities.
Q2. How do LMS platforms protect student data?
FERPA-aligned platforms restrict personally identifiable student information disclosure, implement role-based access limiting who views student records, and define permissible data use in processing agreements. Organizations should verify vendors don’t use student data for advertising or secondary processing beyond the contracted purpose.
Q3. What certifications should an LMS have?
SOC 2 Type II (audited operational security controls), ISO 27001 (information security management), and FedRAMP for US government use. Healthcare deployments require a signed Business Associate Agreement (BAA). Certifications indicate audit coverage but don’t eliminate organizational access governance responsibility.
Q4. Can LMS data be deleted permanently?
GDPR Article 17 grants data subjects the right to erasure under specific conditions. Compliance training completion records may need retention as regulatory evidence even when personal data is deleted, these obligations can conflict and require legal guidance to resolve.
Q5. Who is responsible for LMS security?
Shared: the LMS vendor owns platform infrastructure (in SaaS deployments); the organization owns identity management, access governance, and data classification. “The vendor handles security” is not a complete answer. Data processing agreements define contractual responsibilities; internal policies define operational ones.